It’s been about a week since I decided to become a security-focused developer, and already clear change is afoot. I’m excited about what’s coming. However, it’s not been without some challenges.
But first, the good parts.
As I noted in my last post, I laid out a simple plan for transitioning to being a security-focused software developer.
If you missed that post, here’s the list:
- Build up a solid security-focused RSS feed.
- Build a collated collection of security-focused podcasts.
- Build a collated collection of security-focused blogs.
- Find a good list of security-focused books.
- Renew my PluralSight subscription and work through as many security-focused courses as possible, over the next 12 months.
- Continue writing with a security focus for Sqreen, Codeship, and ownCloud.
This one, I’ve started in earnest!
In the list, I already have:
I’ve already gotten into the groove of what’s happening in the world of security.
It’s a solid, initial, list, one which I’m sure it will progressively evolve.
I’ll step through the progress I’ve made since then in just a moment.
But first, while I can’t give much away yet, I may already have the opportunity to move into a more security-specific role.
More as and when that comes to hand.
Build a Collated Collection of Security-focused Podcasts
The collection of security-focused podcasts, well that one’s not been actioned yet.
I’m going to put that down to it just slipping by, or “the dog ate my homework miss” type of excuses as to why it’s not happened.
The same goes for taking action on building a collated collection of security-focused blogs.
However, does it?
Not really, as the RSS feed is the same thing.
So come to think of it, I should remove that from the original post.
Find a List of Security-focused Books
As for finding a good list of security-focused books, well, through a chance conversation with two colleagues at one of my primary clients, I’ve been put onto an excellent one.
It’s called PHP-Sicherheit (PHP Security).
It turns out a colleague of mine, Peter Prochaska, is a co-author.
However, I’ve so many books on the go, that I’m a little reluctant to start it until I’ve completed the first two.
But when I’ve finished them, I’ll be getting into it.
As a side bonus, it’s going to help me improve my German language skills!
Renew My PluralSight Subscription and Learn
I’ve taken action on this item!
And I’m very proud that I have.
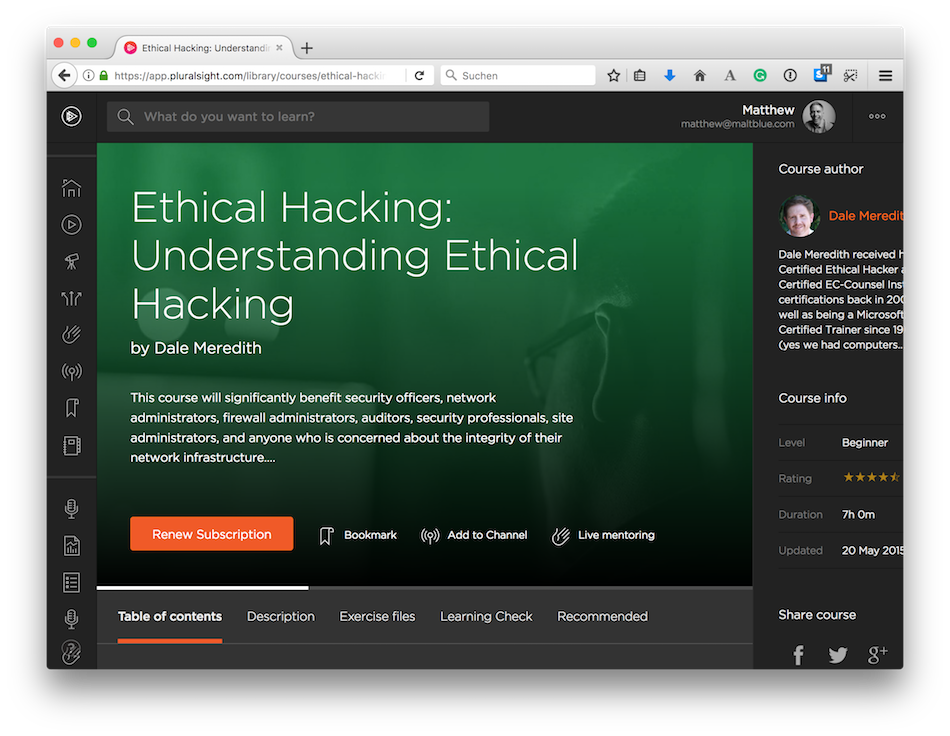
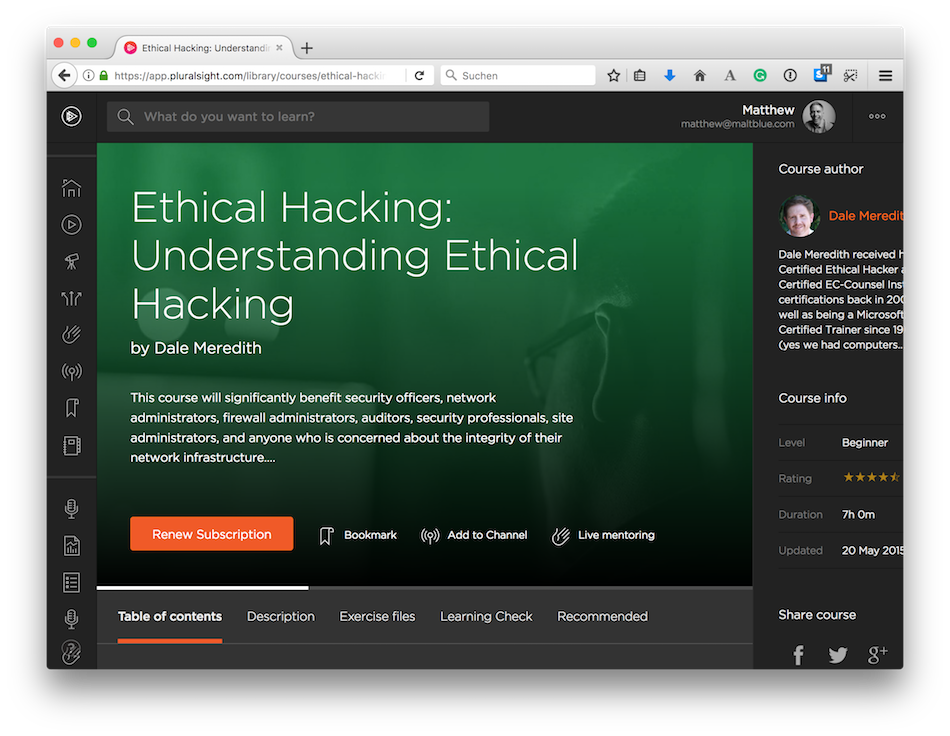
As I’m a Pluralsight author, it made sense to me to look to them first for courses on security.
Perhaps oddly, even though I’m an author on their platform, I’ve never taken a course with them before.
But since the last post, I’ve gone through and bookmarked a series of courses that seemed to fit what I need to learn, and have begun in earnest, working through Ethical Hacking by Dale Meredith.
Man, what a find!
Here’s the course’s description:
This course will start you down the path of becoming an Ethical Hacker, or in other words; become a “Security Profiler.” You will learn to start thinking and looking at your network through the eyes of malicious attackers. You will learn to understand the motivation of an attacker. It is the duty of all System Admins and Security Professionals to protect their infrastructure from not only outside attackers but also attackers within your company. We will cover the terminology used by attackers, the difference between “hacking” and “ethical hacking”, the phases of hacking, the types of attacks on a system, what skills an Ethical Hacker needs to obtain, types of security policies, why Ethical Hacking is essential, how to be in the “know” of what’s happening in the hacking world, who a “hacker” is, what are the biggest security attack vectors, and more. This course is part of the Ethical Hacking Series.
I felt that this was as good a course as any to begin with.
After all, if I’m going to learn how to be able to code securely and harden servers, then you have to understand how they can be hacked, along with the mindset of a hacker.
Secondly, after reading about the Ethical Hacking certification on Troy Hunt’s site, it seemed like a great way to both learn about the topic, and to prepare for a globally recognised industry-standard certification.
More on that another time.
I’d only heard of Dale in passing up until now, so I didn’t know what to expect.
But boy, what a treat!
Allowing for the fact that the course is based around using Microsoft Windows, a platform that I usually try to avoid as much as possible, owing to some atrocious initial experiences many years ago, Dale’s excitement and enthusiasm is infectious.
His style of teaching is so engaging and a little quirky.
Given that, it’s so easy to be carried along by his love of the topic.
I did some further reading about him from his website, and feel that I may have found a kindred spirit in Dale.
His love of comic characters and superheroes reminds me a lot of myself and my childhood.
It also reminds me of my first course with Pluralsight and a talk that I did at PHP World last year.
It was full of references to Ironman, Thor, and The Hulk, among others.
On the course itself, it’s early days so far; I’ve only progressed 215 minutes into the class.
As a result, I’m still in the setup section of the course.
But when I’ve progressed further through the course, I’ll be sharing my experience of it here, in a blog post.
Started Building a Docker Setup Instead of Windows
As I mentioned, Dale based the course around Microsoft Windows.
That makes sense as he’s an experienced trainer in a range of Microsoft products.
However, I’m an open source person, and a big Linux user and advocate.
Given that, and as I tweeted to Dale yesterday, I’m building a Docker container configuration, so that I can follow along on Linux instead.
Now, this might be presumptuous of me that I can do that, as I’m only just at the beginning of the course, but to me it makes sense.
I’m much more experienced with Linux and the command line and feel that by substituting as necessary, that I’ll get a lot more out of the course, than trying to learn a lot of Windows knowledge at the same time.
After all, my focus is on hacking, not a particular operating system.
I’m not taking a shot at Windows, nor Microsoft.
But using Linux seems like a more logical, practical, and intuitive approach.
Learning by Doing (an app rewrite)
As I’ve been watching the course, and during my daily exercise sessions, I’ve been wondering if re-writing a small application of mine would make sense as yet another way to learn about secure software development.
Perhaps I’m just overly enthusiastic.
Okay, I’ve wanted to rewrite it for some time.
But, genuinely, it seemed like a practical thing to do.
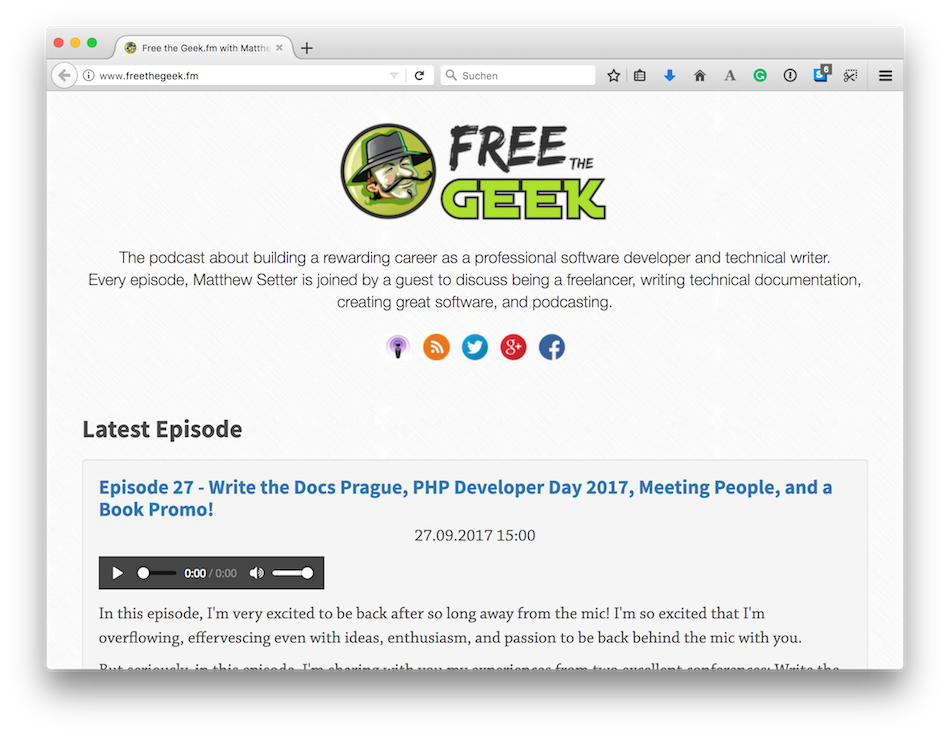
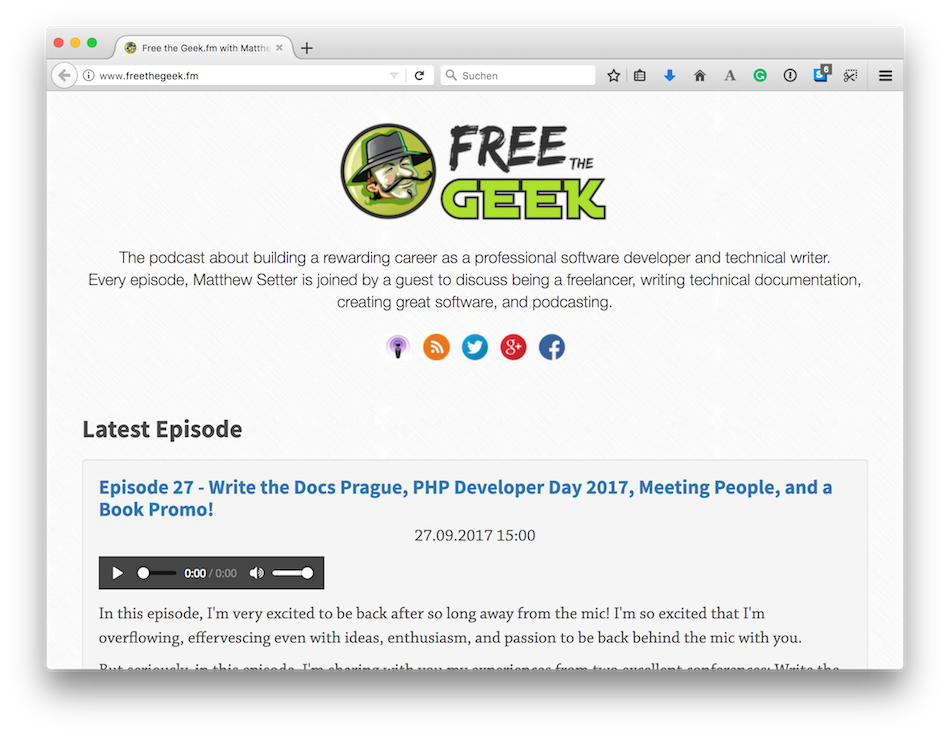
As some background, I wrote a simple website for one of my podcasts, Free the Geek, using the Slim Framework (for PHP).
There’s nothing wrong with the code - hence my wondering if rewriting it is the correct approach.
But, I thought:
- What if I start, largely, from scratch; what could I do and learn?
- What if I took security as a baseline, core, configuration, just like testing?
If I started over, effectively a green-field project, then I could think through the entire stack, as well as the application, from a security standpoint.
What I mean by that is that I could consider:
- How the application’s hosted
- Where it’s hosted
- How the CI/CD pipeline’s built
- How the app’s built
That way, I could build it with security baked-in at every point in the process.
To that end, here’s what I’m thinking (thanks to Mark Railton (@railto) for encouraging me to blog about this).
The application’s being re-built in my favourite software development framework: Zend Expressive.
Besides writing a book on Zend Expressive, it’s a framework that I’ve been passionate about for some time.
I love it because it’s very well designed and quite light-weight.
As well as that, I’ve not used it for some time, primarily because of spending so much time doing technical writing, that I’ve been itching to get back to it, and get stuck in and do something practical with it.
So you can see that perhaps I’d made the decision to code in the framework, and learning security was how I was attempting to justify to myself the decision that I’d made.
That admission aside, it still makes sense to me.
I could ramble on all day about Zend Expressive.
Or I could say that it will give me lots of new things that I can share on Master Zend Framework.
Development and Deployment
Now let’s consider the environments in which it will be developed and deployed.
It’s going to be deployed as a Docker container, to DigitalOcean, using a combination of Docker commands.
I made that choice because I love how compact Docker is, both for development and deployment.
I also love how little you have to do to design and build an image, to deploy it, and to update it.
Sure, Docker’s not perfect, but from speaking to people at Docker, they said that they are aware of these issues and are progressively working to fix them, and to make them both more consistent and intuitive.
Hats off to them for that.
The final reasons why I’m using Docker is that Docker is a technology that I’m passionate about excelling at, plus it’s scriptable as part of a CI (Continuous Integration) and CD (Continuous Deployment) pipeline.
I write a lot about said pipelines for Codeship, so I’m going to use them to create one for the project.
What I’m thinking at this stage is that the process will go something like this; on every push to the remote (GitHub) repository, whether develop or master, Codeship will clone the repository, and run the tests.
If they pass, then it will build a new Docker image, store that image in my account on Docker Hub, and then run a script that deploys the new image to my droplet on DigitalOcean.
I’ve done all these things manually before, so I’d suggest that it shouldn’t take a lot to script them up.
This could be either as a script that I can create via the Codeship pipeline UI or a build script that I can include in the repository, that the pipeline can run.
Having said all this, I’ve meant to learn more about Codeship’s Docker integration for some time.
So this is an excellent, and practical way of doing that.
At this stage, I don’t have that much more to say about the design.
It’s a simple site that reads podcast episode data from files on the filesystem.
The files are a combination of Markdown and YAML front-matter.
It uses a filesystem cache.
As a way of increasing it’s complexity and sophistication, along with potential attack vectors that have to be learned about and defended against, I’m thinking of using Redis instead of the filesystem for caching the episode data and possibly using a database as well.
But doing so doesn’t make a lot of sense, as it doesn’t need that level of complexity.
Plus, it would degrade the content creation workflow.
I’m also adding a logging component, which will help with debugging, should it be required.
For that, I’m planning to go with Loggly.
I could set up Elastic Stack.
But at this stage, a SaaS, such as Loggly, makes more sense
Just for transparency, I write for Loggly.
Trouble/Challenge Keeping Focused / Letting Other Things Go
You might have picked up from that last section, that I’m very energetic — despite, or in spite of having a young family.
And that’s the trouble with doing well at anything because to excel at something, you have to be focused.
You have to put a lot of other things aside, so they don’t distract you from what you need to do.
You have to avoid the shiny, distracting things.
These things can seem so entertaining and important.
For me, that’s always been a challenge.
It’s something that doesn’t come easily.
But, if the past week’s anything to go by, I think that by spending at least 30 minutes a day going through a course on Pluralsight, or reading a relevant blog post or book, or listening to a related podcast, learning security will stay top of mind.
I believe that these activities will continue to remind me of what my new focus is, why I’m doing it, and continue to provide enthusiasm and motivation to press on and not be distracted by anything else.
If you have suggestions, I’m all ears.
What do you do to stay motivated?
Podcast Changes

Okay, one last thing.
I’ve stopped and started and stopped and started with my Free the Geek podcast.
What is it about, what should it be about, am I good enough, etc.
Well, after a long walk yesterday, I’m keen to continue with it.
But it has to stay relevant to what I do on a regular basis.
Otherwise I’ll lose interest in it.
So, I’m shifting gear with it, and going to make it more of a reflection of what I’m learning and doing on a regular basis.
Given that, it’s going to shift tack and have a more significant security component in it.
I’m hoping to get some different security-related professionals on over the coming months so that I can pick their brains.
This is a technique that I picked up from Sammy K. Powers.
That way, we can both learn and grow quickly.
And that’s a wrap
That’s right, after 2,417 words, we’re done.
It’s still new, but this new journey’s one that I’m, clearly, very excited about.
If you’re thinking of doing the same thing, I encourage you to do it, but to put a basic plan in place that you can use to ensure you’re on track, that you’re making progress, and that will help you avoid any pointless, trivial distractions.
Don’t just free-wheel it.
Make a plan, and let that plan help you take action so that you can learn and grow your career in the best direction you can.
Until next week, have a great week.
Matt






Join the discussion
comments powered by Disqus